How XOR Three-Shard Encryption Protects Your Private Keys (Visual Guide)
- Why Private Key Protection Is Everything
- What Is XOR? Core Principles in 3 Minutes
- Three-Shard Encryption: How ArcSign Protects Your Keys
- Signing Flow: How Your Key Briefly "Appears"
- Encrypted Wallet Backup (.arcsign): Safer Than Pen & Paper
- XOR Sharding vs Other Key Protection Methods
- Attack Scenario Analysis
- FAQ
Why Private Key Protection Is Everything
In the crypto world, there is a well-known saying: "Not your keys, not your coins." Your private key is your proof of ownership. Whoever controls the key controls the assets. There is no bank to freeze your account, no customer support to reset your password. Once a private key is compromised, your funds are gone — permanently.
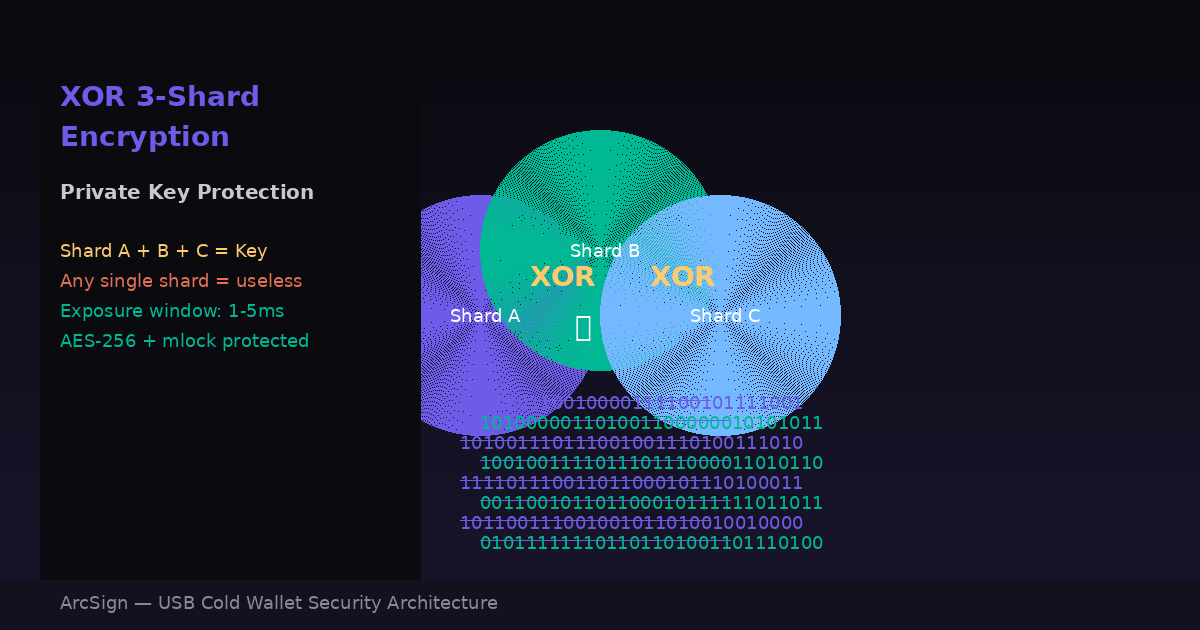
Yet most wallet software simply encrypts the private key with a single password and stores it on disk. If your computer is compromised and malware reads the wallet file, the attacker only needs to crack one password to take everything. ArcSign takes a fundamentally different approach: XOR three-shard encryption ensures your private key never exists in complete form in any single location.
ArcSign's security principle: If a private key never exists in complete form, it cannot be stolen. XOR three-shard encryption is the mathematical foundation that makes this possible.
What Is XOR? Core Principles in 3 Minutes
XOR (Exclusive OR) is one of the most fundamental bitwise operations in computer science. The rule is simple: when two bits are the same, output 0; when they differ, output 1. This sounds basic, but it has a property that is extraordinarily important in cryptography.
XOR Truth Table
The cryptographic magic of XOR lies in its perfect reversibility: if A XOR B = C, then C XOR B = A, and C XOR A = B. More importantly, if B is a completely random value, then even knowing C, it is impossible to derive A without knowing B. This is the principle behind the One-Time Pad — proven to be information-theoretically unbreakable.
A Simple Numeric Example
Suppose your "private key" is the number 42 (binary: 101010). Let's use XOR to protect it:
Now you store 53 and 31 separately. Even if an attacker obtains either number, they cannot determine that the original key was 42. Only by having both shards and computing 31 XOR 53 can the original be recovered. ArcSign extends this concept to three shards for even greater security.
Three-Shard Encryption: How ArcSign Protects Your Keys
The moment you create a wallet, ArcSign executes these three steps to protect your private key:
A cryptographically secure random number generator (CSPRNG) creates two completely random shards — Shard A and Shard B — each the same length as the private key. These shards have no mathematical relationship to the key; they are pure random data.
Shard C is computed as: Private Key XOR Shard A XOR Shard B. Once calculated, the original private key is immediately wiped from memory. Only three seemingly random data fragments remain.
Each shard is individually encrypted with AES-256-GCM and stored in separate locations on the USB device. Any single shard viewed in isolation is meaningless random data — no shard reveals any information about the private key.
The security of XOR three-shard encryption does not rely on algorithm secrecy or key strength. It is based on information theory itself: any combination of fewer than three shards provides zero information about the original private key. This is mathematically provable.
Signing Flow: How Your Key Briefly "Appears"
When you need to sign a transaction, the private key must be briefly reconstructed. ArcSign minimizes the risk of this moment:
Before reconstruction, ArcSign requests a protected memory region from the OS and locks it with mlock, preventing it from being swapped to disk. Even if the computer loses power, no trace of the key will remain on the hard drive.
The three shards are XOR'd together in protected memory: Shard A XOR Shard B XOR Shard C = Original Private Key. This computation takes less than 1 millisecond since XOR is the lightest bitwise operation available.
The reconstructed key signs the transaction. The moment signing completes, the entire memory region is overwritten with zeros and released. From reconstruction to destruction: 1–5 milliseconds.
Even if an attacker could monitor your computer's memory in real time (already an extremely difficult attack), their window of opportunity is mere milliseconds. By contrast, many wallet applications keep the decrypted private key in memory for the entire duration the app is running.
Encrypted Wallet Backup (.arcsign): Safer Than Pen & Paper
When it comes to key security, backup is equally important yet often overlooked. Traditional cold wallets require you to write down a 12-word seed phrase with pen and paper — but this approach has serious problems:
| Factor | Pen & Paper Seed Phrase | ArcSign .arcsign Encrypted Backup |
|---|---|---|
| Water / Fire Resistance | ✗ Paper is fragile — water, fire, fading | ✓ Digital file, easily backed up in multiple locations |
| Encryption | ✗ No encryption — anyone who sees it can steal your funds | ✓ AES-256-GCM encrypted — unbreakable even if obtained |
| Transcription Errors | ✗ Handwriting mistakes can make recovery impossible | ✓ Digital export — zero transcription errors |
| Backup Cost | Multiple copies = multiple exposure risks | ✓ Multiple copies are safe (encrypted) |
| Recovery | Manually enter 12 words one by one | ✓ One-click import + enter password = full restore |
ArcSign offers an exclusive .arcsign encrypted wallet backup file. With one click, you export a backup encrypted with AES-256-GCM + Argon2id. Store it on a second USB drive, an external hard drive, or even a memory card in a safe. Even if someone else obtains this backup, they cannot decrypt it without your password. When you need to recover, simply import and enter your password — all wallets and settings are restored instantly.
We recommend keeping both your seed phrase (sealed in paper, stored securely) and a .arcsign backup file (on a second USB, stored offline). These two methods serve as redundant backups, ensuring you can recover your assets under any circumstance.
XOR Sharding vs Other Key Protection Methods
Several private key protection technologies exist today. Here is how they compare:
| Method | Principle | Strength | Risk |
|---|---|---|---|
| Single Password Encryption | AES encrypts the full key | Simple to use | If password is cracked, everything is lost |
| Secure Element (SE) | Hardware isolation | Physical-layer protection | Must trust manufacturer; supply chain risk |
| Shamir Secret Sharing | Polynomial interpolation M-of-N | Flexible threshold recovery | Complex implementation; potential bugs |
| MPC (Multi-Party Computation) | Distributed signing | Key never fully appears | Communication latency; requires nodes online |
| XOR Three-Shard (ArcSign) | XOR + mlock + distributed storage | Information-theoretic security, zero latency, works offline | Requires all three shards |
ArcSign's XOR three-shard approach strikes the best balance between security, speed, and simplicity. It requires no special hardware, no internet connection, and no complex mathematics — yet provides information-theoretic-level security guarantees.
Attack Scenario Analysis
Scenario 1: USB Stolen or Lost
An attacker obtains your USB drive. They find three AES-256 encrypted shards. Even if they could break the AES encryption (currently considered impossible), they would only have three random data fragments. Without ArcSign's reconstruction logic, they cannot correctly combine them. More importantly, each shard individually contains zero information about the private key.
Scenario 2: Computer Infected with Malware
Malicious software attempts to read the private key from memory. But the key only exists in mlock-protected memory for 1–5 milliseconds and is never swapped to disk. The malware would need to breach the OS memory protection mechanism within this precise millisecond window — an extremely difficult feat in practice.
Scenario 3: Firmware Backdoor
This threat applies to hardware wallets but is completely irrelevant to ArcSign. ArcSign runs on standard operating systems using generic USB devices — there is no proprietary firmware, so there is no firmware backdoor attack surface. Your security comes from open, verifiable cryptographic algorithms, not from "trusting" closed hardware.
XOR three-shard + AES-256-GCM dual-layer encryption + mlock memory protection + USB offline storage = multi-layer defense. An attacker would need to breach every single layer simultaneously to access your private key — practically impossible.
Frequently Asked Questions
Q: Is XOR encryption secure? Can it be brute-forced?
When combined with truly random keys, XOR is information-theoretically unbreakable (the One-Time Pad principle). ArcSign uses a cryptographically secure random number generator (CSPRNG) to produce shards, ensuring each one is fully random. Even if an attacker obtains one or two shards, it is mathematically impossible to derive the original private key.
Q: How is ArcSign's three-shard approach different from Shamir Secret Sharing?
Shamir Secret Sharing (SSS) uses polynomial interpolation and supports M-of-N threshold schemes (e.g., any 3-of-5 shards can recover the secret). ArcSign uses a strict 3-of-3 XOR scheme — all three shards are required. This design is simpler, more secure, and avoids implementation vulnerabilities that can hide in complex mathematics. All shards stay on the same USB device and are managed automatically by ArcSign.
Q: What if my USB gets damaged or lost? How do I recover?
ArcSign provides two recovery methods: (1) Use your 12-word seed phrase to rebuild on a new USB, or (2) Import a .arcsign encrypted backup file with one click. We strongly recommend exporting a .arcsign backup to a second USB immediately after wallet setup. Even if someone else obtains the backup file, they cannot decrypt it without your password.
Q: Does XOR three-shard encryption slow down transaction signing?
Not at all. XOR is one of the lightest bitwise operations — recombining three shards takes under 1 millisecond. The entire key exposure window (reconstruction through signing to memory wipe) is kept within 1–5 milliseconds. Users experience zero perceptible delay.
Protect Your Crypto Assets with Math
Download ArcSign for free and experience the peace of mind of XOR three-shard encryption.
Download ArcSign Free